private key algorithm
The private key method is a cryptographic method for the encryption and decryption of sensitive data that must be protected from unauthorized access.
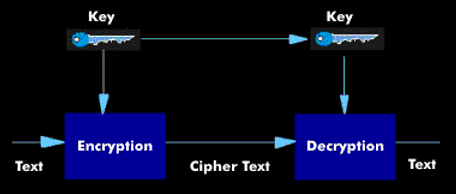
This method is a symmetric encryption in which only one secret cipher key is used for encryption and for decryption. Whoever is in possession of this key can generate the corresponding ciphertext from plaintext information and vice versa from the ciphertext the plaintext. Before encryption or communication, the key must be exchanged between the communication partners via a secure channel. Thus, the security of the private-key method essentially depends on the secrecy of the cipher key. One of the better-known private key authorization methods is Kerberos.