vulnerability
A vulnerability is a security hole in information security. It can pose a threat because it allows intruders to access system resources and manipulate or steal data.
The security vulnerability is usually a flaw in the software that can be exploited by hackers and allow them to access systems or networks. In the context of Common Vulnerabilities and Exposures( CVE), vulnerability is about an attacker violating the security policy of an IT system.
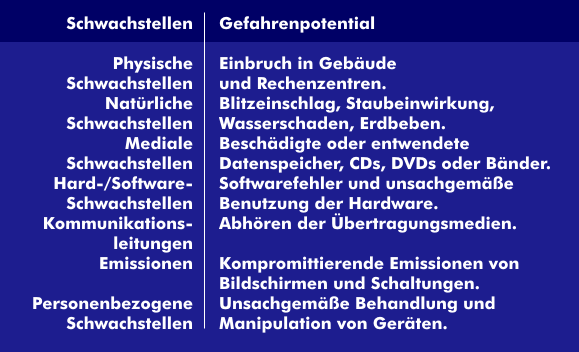
Vulnerabilities can have physical or natural causes such as breaking into a computer room, water or dust getting into pipes or into servers and storage units thereby limiting functionality or rendering the computer inoperable. The physical transmission media can also create vulnerabilities. They can be tapped or, in the case of optical fibers, even bent to such an extent that parts of the light signal leak out. Poorly trained employees can also become weak points due to human error or incorrect instructions. The company organization can cause errors through faulty processes, as can technical deficiencies in the communication components. With the vulnerability analysis, employees in vulnerability management can record and rectify the critical points of information security.
Vulnerability Management( VM) develops procedures and processes to identify and eliminate security-relevant vulnerabilities in IT systems. To this end, security experts, service companies offering Hacking as a Service( HaaS) or commissioned white-hat hackers detect security vulnerabilities that can be remedied via vulnerability management.