trusted platform module (TCPA) (TPM)
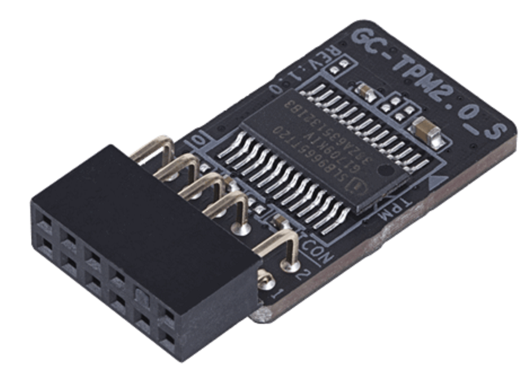
The standard for a security management subsystem developed by the Trusted Computing Group( TCG) is called a Trusted Platform Module (TPM). These modules are implemented as a system-on- chip( SoC).
The Trusted Platform Module is a microchip with which manipulations to software can be detected. For this purpose, the TPM module collects and stores data about trusted, externally executed software. If the TPM module detects changes to features on the software, it denies access to the key used to encrypt and decrypt the data. Using the public key method, TPM modules support the chip-internal generation of key pairs, public key signing, encryption and decryption for the secure storage of data. In addition, the TPM module performs the functions of an Endorsement Key (EK), which can be used to anonymously create an identity key generated in a TPM module.
The TCG software stack provides a standard API for accessing TPM functions. This software specification allows application developers to develop applications that generate a cryptic key.
TPMs can be used in mobile and stationary computers, in communication and terminal devices. For example, in PDAs, smartphones, tablets and personal computers, in cell phones, set-top boxes and transmission components. They are part of the Windows Vista security strategy, among other things.