trojan
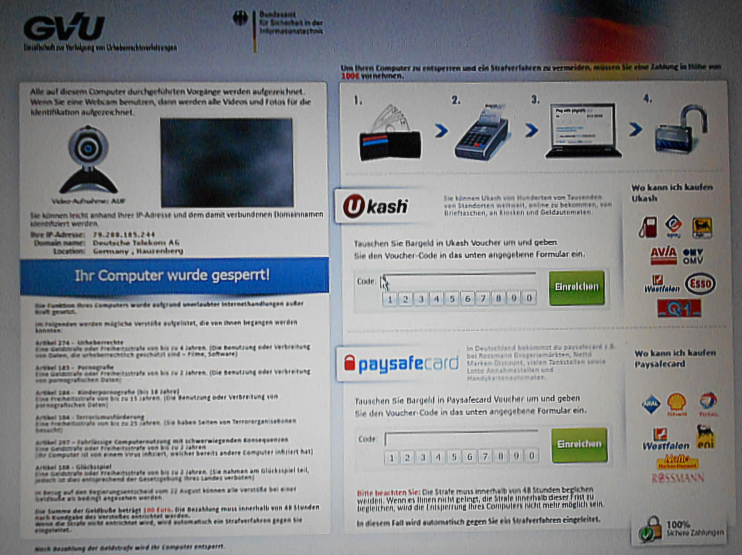
A Trojan, also referred to as a Trojan horse, is malware that is designed to appear as a legitimate program and thus gain access to the system. It has other, unknown functions in addition to its actual function.
Trojans cause damage "from the inside". As with rootkits, they spy out data files and passwords and send them over the Internet, but they also change or delete system configurations. They abuse computers and retrofit them with additional functions with which they capture access data, passwords and serial numbers or impair remote properties and system administration, for example as spyware, for sending out spam or for attacks on servers.
Trojans spread via email attachments, but also via file sharing networks.
Trojans can be prevented by not downloading and opening mail attachments from unknown e-mail addresses, as well as not downloading software from unknown sources onto your computer, or at least checking them first with a virus scanner.
A special Trojan is the federal Trojan, also known as the state Trojan. It is generated by government institutions and is supposed to spy on suspicious computers.