token
The term token is used in different contexts. On the one hand in network technology for a bit pattern with control data that can be read by the connected stations, on the other hand for a cryptographic bit pattern for generating encryption.
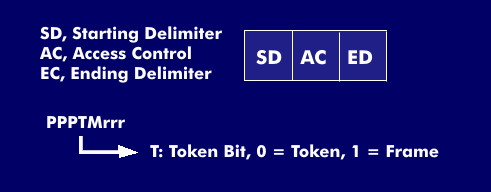
- A token is understood to be a bit pattern that continuously traverses a ring network in one direction, which operates according to the token ring method. In the Token Ring, the token is a defined bit pattern, of three bytes in length. It consists of the starting delimiter( SD) and the ending delimiter( ED), both one byte long, with the access control field in between, which also has the length of one byte. The access control field occurs both in the token and in the token ring frame. By means of the token bit, which is the fourth bit of the access control field, a station can recognize whether it is a token (free token) or a frame (busy token). In addition, the access control field contains the monitor bit for control purposes as well as three bits for priority information and three reservation bits that perform priority control of the next free token.In a token bus, the token is passed on as a send right from a station to the physically or logically defined successor station. If there is no need to transmit, it is again passed on to the specified successor station.
- The FDDI to ken is similar to the token ring token, but it consists of four data fields: The Preamble( PA), the Starting Delimiter (SD) followed by the Frame Control( FC) and the Ending Delimiter (ED).
- For encryption, we refer to a cryptographic token, a smart card or chip card on which cryptographic information is stored and which supports encryption functions. In conjunction with a user name and password, tokens are a widely used method of authentication. The token can come in a variety of designs and different connection options: As a token card, USB token, key fob or as a software token that emulates the function of a hardware token.
- The term token also exists for cryptocurrencies. This is a unit for financial transactions. Only the one who owns a valid currency token can execute a transaction on the blockchain. Such a transaction can be a payment with a cryptocurrency or another decentralized application. A valid token ensures that only authorized participants can execute transaction or other decentralized applications(dApps). Currency tokens represent the current value of the corresponding cryptocurrency Bitcoin or Ether.
- In financial transactions, there are tokens that can be exchanged for other tokens; however, others are not exchangeable. Exchangeable tokens are fungible tokens. These include the tokens of cryptocurrencies such as Bitcoin. They are exchangeable because one Bitcoin has the same value as another Bitcoin. Tokens that are not exchangeable are non-fungible tokens(NFT). They are used, for example, to indicate the value of unique assets such as art objects.