phishing
With the neologism phishing, which is a combination of password and fishing. It is a technique with which fraudsters fish for passwords. The attackers are called phishers and attempt to retrieve confidential banking data - such as the personal identification number( PIN), transaction numbers( TAN) or credit card numbers - from bank customers via the Internet and use them to carry out financial transactions. Banks have responded to this with improved transaction procedures such as the electronic transaction number( eTAN) and the ChipTAN procedure.
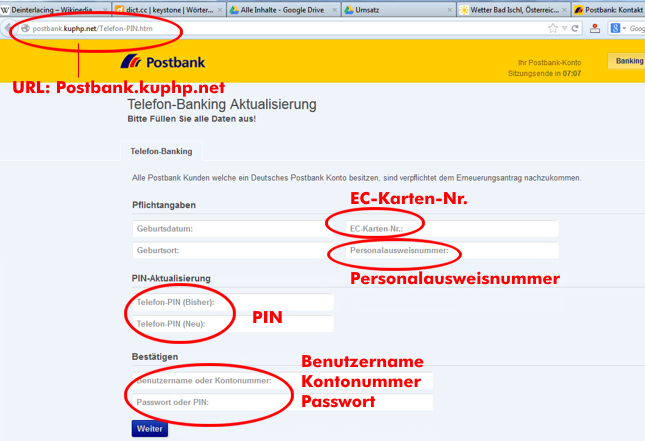
In phishing, phishers use fake bank homepages to request confidential information. For this purpose, a fake homepage of a financial institution is placed on the Internet. E-mails with a link to the fake homepage are sent at random. These e-mails discuss security or banking-related issues with the instruction to perform a certain action that will benefit the attacker. The phisher wants to trick the victim into clicking on a malicious link, opening an infected attachment, authorizing a money transfer or visiting a certain website. Details that the victim enters into a replicated homepage, such as personal identification numbers and transaction numbers, are filtered out and immediately available to the attackers for unauthorized financial transactions on the correct homepage.
Other phishing techniques
Since phishing no longer yields the hoped-for success due to improved transaction procedures, it has been refined into spear phishing. With this method, victims are targeted by phishers posing as old acquaintances and using harmless information from social networks. The phishers use the trust built up in this way to click on a link via forms to download ominous software.
Another technique used by phishers is the use of malware, which is introduced as a Trojan into the communication link between the bank and the bank customer, where it grabs the data. The phishing technique is often used in social engineering attacks.