malware
The generic term malware, which is a word creation from the words malicious software, is understood to mean malicious malware that impairs IT security and the functionality of computers and systems. Specifically, the many manifestations of malicious software include viruses, Trojans and worms, flooding, DoS and DDoS attacks, spyware, badware, spams, hoaxes, rootkits, etc.
Malware can be used to spy, tap, modify or deletedata, and the various functions are not desired by the user and are done without their consent. Malware techniques also include evasion and obfuscation attacks, which are used to deceive users and security administrators. The technical methods used by malware aggressors to spy on their victims are of a high technical level. Users can recognize the infestation of their computer by a sudden loss ofmemory capacity or by a rapid decrease in computing speed. Virus scanners and anti-malware software are available as technical tools. The attackers ' goal can be to manipulate or steal data, to access accounts, or to affect the functionality of computers.
Malware can be detected by virus scanners. Common antivirus and anti-malware programs are often unable to detect or track attacks. Once the malware attacks have done their job and spied out design plans, account numbers, access credentials or other information, the programs cover their own tracks. Often, the damage done and the intrusion can only be reconstructed after the private individual or company has already been harmed.
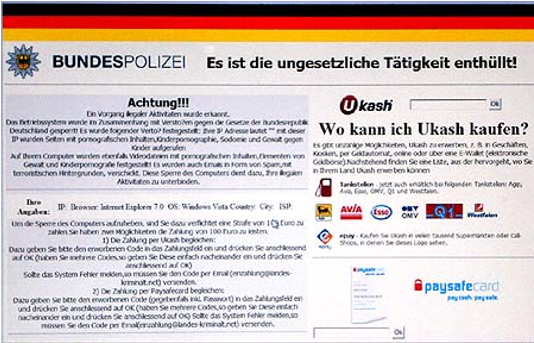
A well-known malware is the federal Trojan that completely locks Windows computers so that no functions can be entered. These Trojans are sent as ransomware Trojans and belong to ransomware, which stands for extortion software or ransomware.