firewall design
In terms of concept, firewalls are divided into different access techniques such as packet filtering, stateful inspection firewalls( SIF) and proxy firewalls. In addition, there are interesting security systems that consist of various firewall concepts and the cloud serviceFirewall-as-a-Service( FWaaS) offered by cloud service providers.
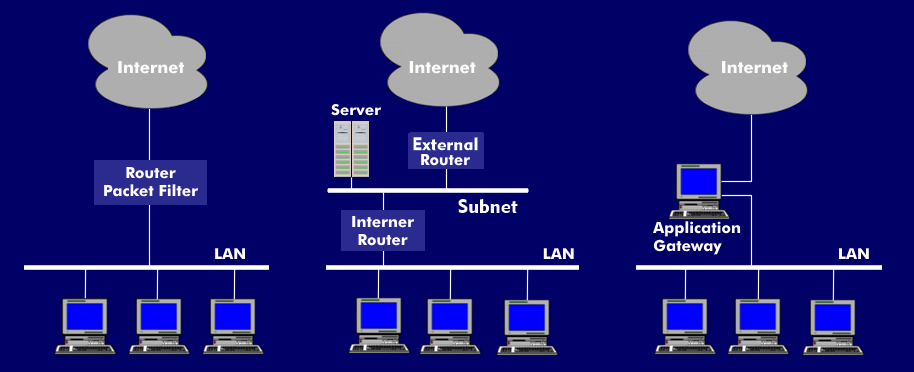
The different firewall concepts
A simple firewall configuration uses packet filtering, in which incoming and outgoing data packets are analyzed and controlled at the link layer, network layer and transport layer using an existing table. In this configuration, a packet filter interprets the content of the data packets and verifies that the data in the corresponding communication control layerheaders conforms to the defined rules. The packet filters are transparently inserted into the line.
The circuit relay concept works with a subnet and two routers, an external and an internal router, and a host as the connection partner through which the communication takes place. The circuit relay concept is similar to the packet filter, but they operate at a higher level of the protocol stack. The computer that wants to establish a connection must register with the host and prove that it has access authorization. This means that an external user cannot draw any conclusions about the network structures.
The most secure, but also most complex alternative to a firewall is the application gateway, which implements sufficient security mechanisms over several layers. It can logically and physically decouple the networks and expects each user to identify and authenticate himself beforehand. The application gateway receives the data packets at the corresponding ports. If only one service is to be possible via the port, software becomes active on the application server that transfers the packet from one network side to the other network side, a proxy.
A stateful inspection firewall (SIF) operates on a stateful basis andchecks each connection via the TCP protocol for the entire session duration. Traffic is inspected based on available data from previous connections. SIF firewalls create connection tables with important connection data and compare the connection data of the ew connections with the existing connection tables.
Communication via the proxy
From the accessing user's point of view, it looks like he is communicating with the actual server process of the service on a target computer. However, in fact the user communicates with the proxy server, the proxy that acts as an intermediary to both sides, so that no connection is ever established between the target computer and the visitor. Each proxy on the application gateway can provide additional security services specifically for the service it is responsible for. Due to the respective special proxy and the knowledge of the context of a special service, there are extensive security and logging options in the application gateway.
In accordance with the large number of services offered, there are application-specific gateways, for example, for Telnet, e-mail, HTTP, etc. A high-level firewall system intelligently combines several firewall concepts and thus guarantees the highest level of security.