block cipher
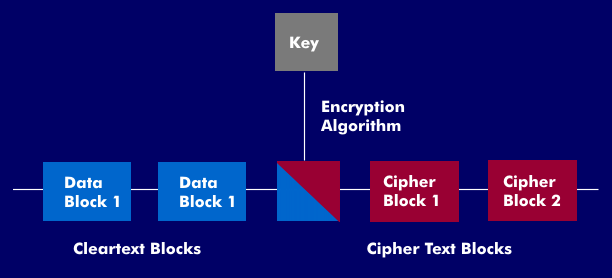
Block cipher is an encryption method in which plaintext is processed in bit groups, i.e. data blocks. The block cipher always works with data blocks of fixed length, for example 64 bits. These data blocks are encrypted and decrypted independently of each other. If a data block does not have the required block length, it is padded with fill bits.
Block ciphers always use the same key for encryption, which can mean that blocks with identical information content also have the same ciphertext block. Some variants circumvent this by creating links between neighboring blocks.
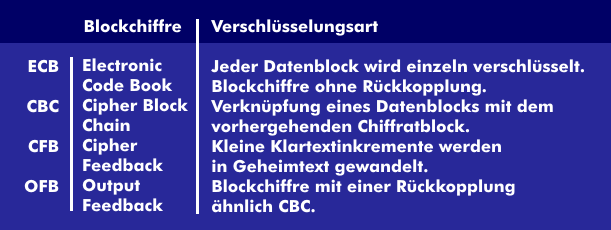
The international standard ISO 10116 defines four different modes of operation for block cipher algorithms: electronic code book( ECB), cipher block chain ( CBC), cipher feedback ( CFB), output feedback( OFB) and counter mode ( CTR).
Block cipher methods such as the Advanced Encryption Standard( AES) or the Data Encryption Standard( DES) work with logical operations such as XOR, substitution, permutation and arithmetic operations ofdual arithmetic. To prevent possible decryption as much as possible, block cipher schemes work in multiple rounds during encryption. One round is intended to provide confusion and dispersion, with confusion making the relationship between ciphertext and key as complex as possible. Dispersion( diffusion) attempts to spread the redundancy in the plaintext over the entire ciphertext. Going through multiple rounds further increases confusion and diffusion.
In addition to the block cipher, there is also the stream cipher, in which the information stream is continuously encrypted character by character. Well-known block ciphers are DES encryption, International Data Encryption Algorithm( IDEA), CAST, Lucifer and RC5 as well as Skipjack from the National Security Agency( NSA).