SYN flooding (TCP)
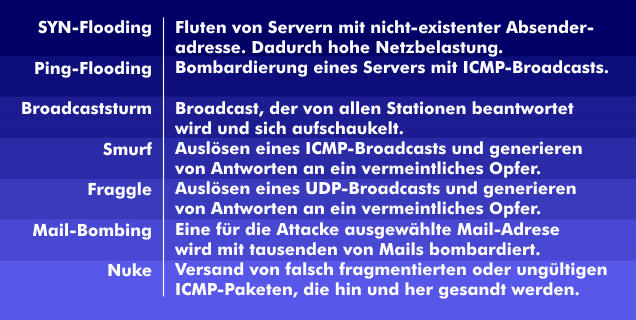
SYN flooding is a DoS attack. It is a targeted attack on a server to overload it and cause it to crash. SYN flooding involves flooding the connection mechanism from the TCP protocol to overload the server with mislabeled TCP data packets.
When establishing a TCP connection, a host sends a synchronization flag to the destination host. The destination computer then sends an acknowledgement of receipt to the initiating computer, whereupon the latter responds with an acknowledgement flag( ACK).
SYN flooding involves flooding the Internet from a host with TCP packets with synchronization flags, using a non-existent source address. Each individual data packet is treated by the dialed server as a connection request. The corresponding server acknowledges the request with an acknowledgement of receipt with the acknowledgement flag set and then waits for the response from the sending terminal.
However, since the source address is incorrect, no response will reach the server. Since the destination computer does not receive a response, it sends another acknowledgement of receipt after some time, and later sends one again, and so on. The connection therefore remains half-open for some time, limiting the number of connections the server can handle. The server becomes overloaded and thus cannot continue to handle even correct requests, and it will continue to do so until the SYN flooding attack is over.