IP security protocol (IP) (IPsec)
IP Security Protocol (IPsec) is a standardization proposal of the Internet Engineering Task Force( IETF) that defines procedures and protocols for multi-vendor secure and protected data exchange using the IP protocol. Standardization activities have been ongoing since 1995. IPSec's standards framework defines the approach for data integrity, content confidentiality, and cryptographic key management. The components of IPSec are the Authentication Header( AH), the Encapsulating-Security-Payload( ESP), the Security Association( SA), the Security Parameter Index( SPI), and the Internet Key Exchange( IKE).
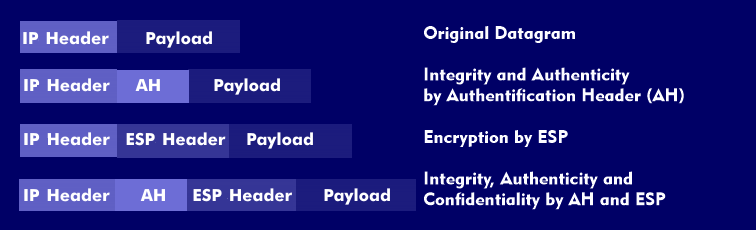
At the beginning of the communication, the procedure used is clarified between the computers involved in the communication and whether the data transmission is to be tunnelled or not. Therefore, depending on the type of encryption, the IPSec framework distinguishes between the Authentication Header-based transport mode and the ESP-based tunnel mode. In the first case, the encrypted Authentication Header (AH), the original IP header is preserved, and the source addresses and destination addresses remain unprotected. The AH header lies between the IP head ers and the transport protocol headers. Authentication is performed using either the MD5 algorithm or the Secure Hash Algorithm( SHA), where authentication involves only the data fields of the AH header, which remains unchanged during transmission. This includes the message content of the AH header, which allows changes to be noticed.
In contrast, the tunnel mode, based on the encrypted ESP payload, provides higher security for the transmitted data packet, since the entire frame is encrypted. The data packet gets a new header in which the source and destination addresses are hidden and only the tunnel endpoints are recognizable.
IPsec for LAN-LAN connections
The IPsec protocol was developed especially for the connection between two LANs. IPsec protects the data packets of the IP protocol against possible modifications and against spying. IPsec does not affect communication protocols or application programs, so Internetworking via routers is not affected. Authentication procedures created using IPsec can distinguish between the data of authorized and unauthorized communication partners. The authorization procedures are based on the MD5 hash algorithms with 128 bits, and the encryption is based on the DES algorithm with 56 bits in Cipher Block Chain( CBC).
IPSec can be used to protect all IP traffic: Transmission Control Protocol( TCP), User Datagram Protocol( UDP), Internet Control Message Protocol ( ICMP), Hypertext Transfer Protocol( HTTP), File Transfer Protocol( FTP), Simple Network Management Protocol( SNMP), Telnet, etc. IPsec is described and standardized in RFCs 1825 to 1829 and 2401.